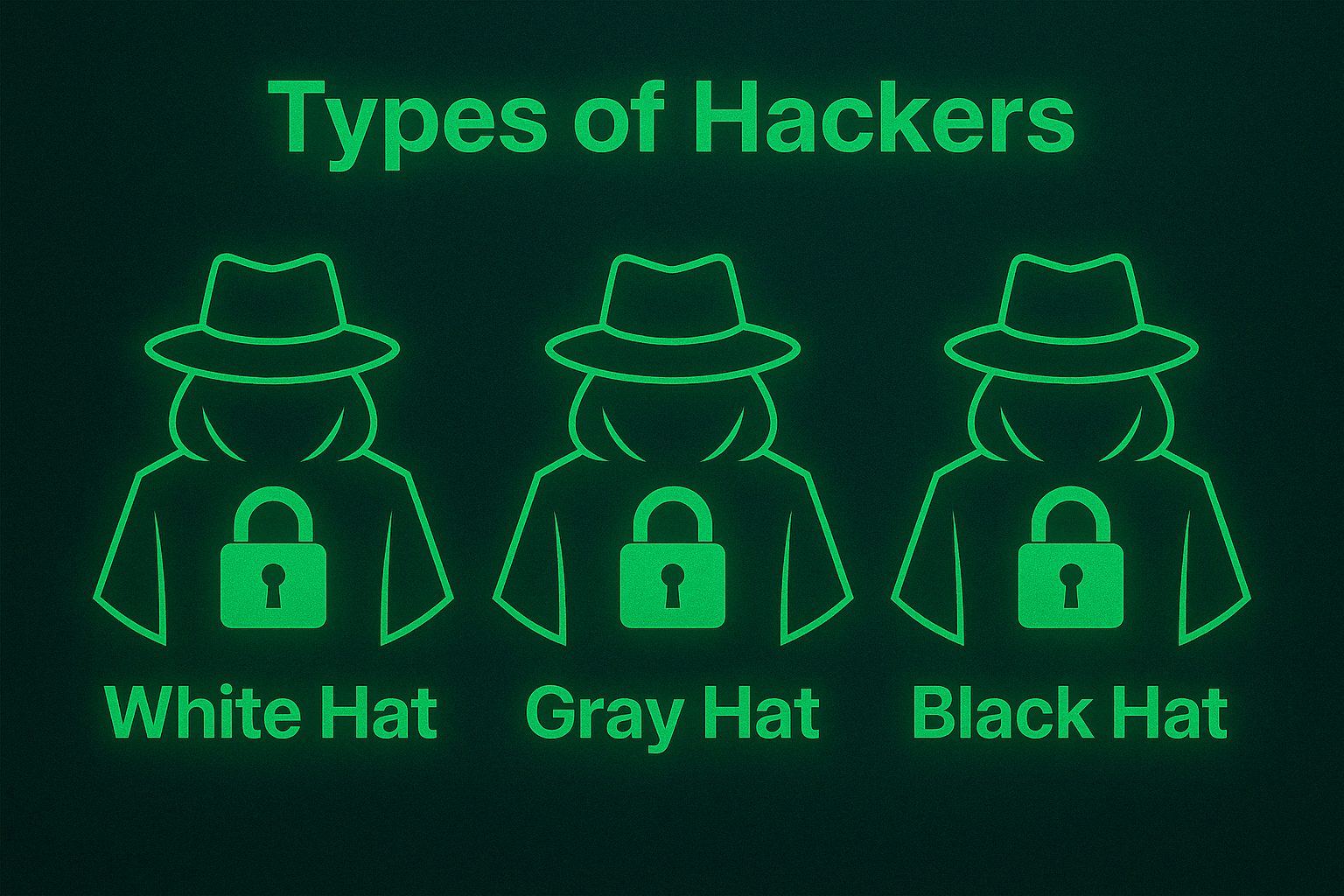
Ethical Hacking vs. Malicious Hacking: Understanding the Differences in a Social Media Context
Explore the critical distinctions between ethical hacking and malicious hacking in the context of social media. This guide delves into the motivations, techniques, and impacts of both hacking types, highlighting how ethical practices can safeguard user data and enhance security, while malicious tactics pose significant risks.